Automated Scanning Tools
In today’s rapidly evolving digital landscape, cybersecurity threats are becoming more sophisticated and frequent. Businesses of all sizes must adopt robust security measures to protect their websites, applications, and networks. Automated scanning tools play a crucial role in identifying vulnerabilities before they can be exploited by cybercriminals. These tools offer a proactive approach to cybersecurity, enabling organizations to detect and mitigate threats efficiently. In this blog, we’ll explore the significance of automated scanning tools, their functionalities, and a detailed analysis of the top ten automated scanning tools, including how Haxore enhances website security.
What Are Automated Scanning Tools?
Automated scanning tools are advanced software solutions designed to assess and analyze websites, networks, and applications for vulnerabilities, misconfigurations, and security risks. They function by conducting systematic scans to identify weaknesses that cybercriminals could exploit. These tools generate detailed reports that prioritize vulnerabilities based on their severity and potential impact.
By automating the vulnerability assessment process, these tools help organizations save time, reduce human errors, and ensure continuous security monitoring. Unlike manual testing, automated scanning is scalable, cost-effective, and capable of providing comprehensive coverage of an organization’s digital infrastructure.
Why Automated Scanning Tools Are Essential?
1. Time Efficiency
Manual vulnerability assessments require significant effort and expertise, often taking weeks to complete. Automated scanning tools perform comprehensive security checks in a matter of minutes, allowing IT teams to focus on remediation rather than detection.
2. Comprehensive Coverage
These tools provide extensive coverage of websites, applications, networks, and APIs, ensuring that every component is thoroughly examined for vulnerabilities. Automated scanners can also assess third-party integrations, cloud environments, and internal systems.
3. Proactive Threat Detection
Automated scanning tools help organizations identify and mitigate vulnerabilities before they can be exploited by attackers. This proactive approach significantly reduces the risk of data breaches, financial losses, and reputational damage.
4. Cost-Effectiveness
Hiring cybersecurity experts for manual penetration testing can be expensive. Automated scanning tools reduce costs by automating the detection process, making security assessments more accessible to businesses of all sizes.
5. Continuous Monitoring
Cyber threats are constantly evolving, and new vulnerabilities emerge regularly. Automated tools provide real-time monitoring and alerts, ensuring that organizations remain protected against emerging threats.
Top 10 Automated Scanning Tools for Website Security
1. Haxore
Haxore is a next-generation automated scanning tool that combines AI-driven insights with real-time security monitoring. It offers:
Comprehensive Vulnerability Detection – Identifies SQL injection, cross-site scripting (XSS), insecure configurations, and outdated software.
Dark Web Intelligence – Monitors the dark web for leaked credentials and sensitive data.
AI-Powered Insights – Prioritizes vulnerabilities based on severity and potential impact.
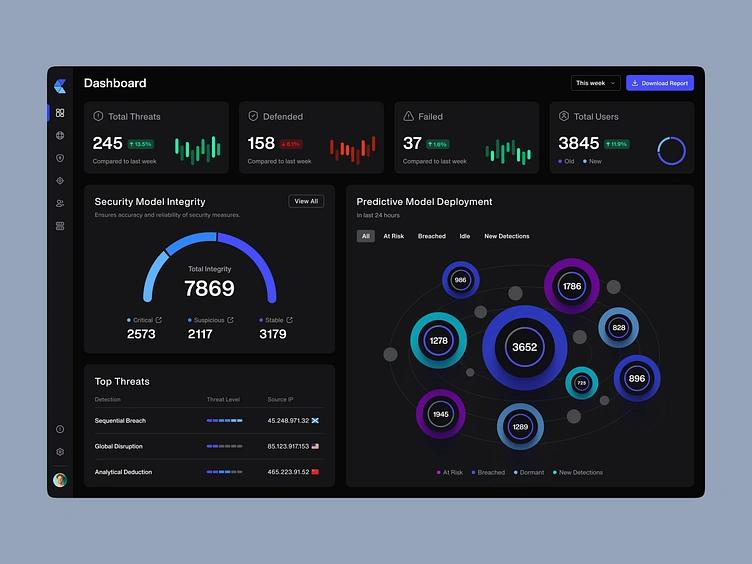
User-Friendly Dashboard – Allows easy configuration, result analysis, and remediation tracking.
Scalability – Adapts to the security needs of both small businesses and large enterprises.
2. Acunetix
Acunetix is a powerful web vulnerability scanner designed to detect security flaws in websites and web applications. Features include:
Automated Security Testing – Scans web pages, APIs, and single-page applications (SPAs).
Extensive Vulnerability Coverage – Detects SQLi, XSS, and misconfigured authentication settings.
Integration Capabilities – Works with DevSecOps tools for seamless security integration.
3. Burp Suite
Burp Suite is a widely used web security testing tool among ethical hackers and security professionals. It provides:
Manual and Automated Testing – Allows both automated vulnerability scanning and manual penetration testing.
Intercepting Proxy – Helps in analyzing HTTP/S traffic and manipulating requests.
Advanced Customization – Users can configure scanning rules and add custom scripts.
4. Nessus
Nessus is a well-known vulnerability assessment tool that helps organizations secure their IT infrastructure. Its features include:
Network and Application Scanning – Identifies vulnerabilities across multiple environments.
Extensive Plugin Library – Supports thousands of plugins for detecting security threats.
Risk-Based Prioritization – Assesses vulnerabilities based on severity and exploitability.
5. Qualys Web Application Scanner (WAS)
Qualys WAS is a cloud-based web application scanner that offers comprehensive vulnerability assessment. Key features include:
Cloud-Based Architecture – Requires no installation, making it easy to deploy.
Deep Scanning – Identifies OWASP Top 10 vulnerabilities and zero-day threats.
Continuous Security Monitoring – Provides real-time threat intelligence.
6. OWASP ZAP (Zed Attack Proxy)
OWASP ZAP is an open-source security scanner designed for penetration testers and developers. Features include:
Intercepting Proxy – Enables manual testing and request manipulation.
Automated Scanning – Detects common web application vulnerabilities.
Active and Passive Scanning – Provides both surface-level and deep security analysis.
7. Nikto
Nikto is an open-source web server scanner that detects vulnerabilities in web applications and servers. Its capabilities include:
Comprehensive Security Checks – Scans for outdated software, misconfigurations, and known exploits.
Support for SSL and HTTP Headers Analysis – Helps identify security weaknesses in encryption and configurations.
Fast Scanning Process – Quickly identifies security issues with minimal resource usage.
8. Intruder
Intruder is a cloud-based vulnerability scanner designed for businesses and enterprises. Its features include:
Automated Security Assessments – Detects vulnerabilities in networks, applications, and cloud services.
Smart Scanning Engine – Provides risk-based vulnerability analysis.
Integration with DevOps Tools – Supports CI/CD pipelines for automated security testing.
9. Rapid7 InsightVM
InsightVM is an advanced vulnerability management tool offering continuous security monitoring. Key capabilities include:
Live Threat Intelligence – Provides up-to-date vulnerability data.
Comprehensive Asset Discovery – Scans entire IT infrastructures for security weaknesses.
Automated Remediation Guidance – Helps teams resolve vulnerabilities efficiently.
10. Tenable.io
Tenable.io is a cloud-based vulnerability management solution that provides:
Web Application Scanning – Detects security weaknesses in web-based applications.
Real-Time Analytics – Offers continuous security insights and threat intelligence.
Integration with SIEM Tools – Enhances security operations and compliance.
Conclusion
Automated scanning tools are essential for modern cybersecurity strategies. They provide fast, accurate, and continuous security assessments, helping businesses safeguard their websites and applications from cyber threats. Haxore, along with other top scanning tools, ensures robust security by identifying vulnerabilities, offering AI-driven risk prioritization, and integrating seamlessly with existing security workflows.
With cyberattacks becoming increasingly sophisticated, investing in automated security solutions is no longer optional—it’s a necessity. Secure your digital assets with Haxore and other leading security tools today.
Related Blogs: